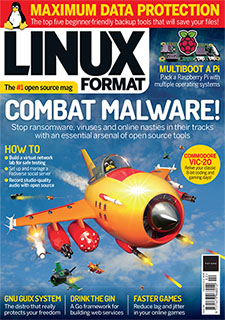
Combat malware the only way we know how with a Tux attack! We investigate malware attack vectors, how ransomware infiltrates systems and how we’ve gone from floppy disk boot viruses to drive-by web browser exploits, so you can better protect your systems.
PLUS: the GNU-loving Guix System, store passwords securely with Swifty, revive the Commodore VIC-20, create rock music effects, record studio-quality audio, test the best backup tools, multi-boot your Pis and more!
Write in now, we want to hear from you! lxf.letters@futurenet.com Send your problems and solutions to: lxf.answers@futurenet.com Catch all the FOSS news at our evil Facebook page or follow us on the Twitters.
